Company Based on UC San Diego Technology Gets Infusion of Capital
A company co-founded by CSE professor and Qualcomm Institute academic participant Ryan Kastner and two CSE alumni is now positioned for new growth thanks to an infusion of capital from a venture-capital firm.
The hardware security company Tortuga Logic just reported receiving $2 million in seed funding, all of it coming from Eclipse Ventures to accelerate engineering efforts and expand sales and marketing. Tortuga Logic offers a suite of hardware design tools to identify security vulnerabilities throughout the process of designing a semiconductor, including Prospect and Unison (used in the semiconductor, aerospace and defense industries). With its new funding, Tortuga Logic will develop new products and increase the feature sets of existing products.
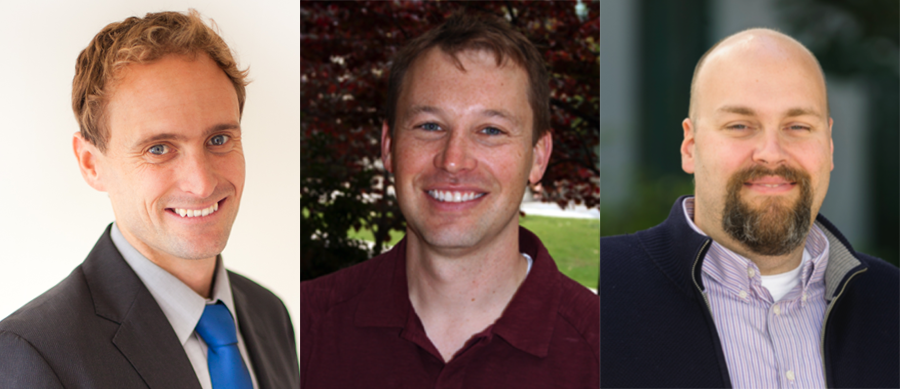
The company's co-founder and CEO Jason Oberg (M.S., Ph.D. '12, '14) also announced on Dec. 14 the hiring of a new VP of Engineering, Andrew Dauman. “We are seeing a huge paradigm shift in cybersecurity,” said Oberg, who co-founded the company while still a Ph.D. student in CSE. “Existing software-based cybersecurity companies address software vulnerabilities but overlook hardware. With a round of seed funding and Andrew Dauman’s leadership, we are fully prepared to take on the challenge of eliminating hardware vulnerabilities.”

Tortuga Logic's technology, based on previous research carried out in the lab of CSE professor Kastner at UC San Diego, identifies and prevents security vulnerabilities in system-on-chip (SoC) designs. Its patented technology augments industry-standard verification tools to enable a secure development lifecycle.
The company was co-founded by experts and pioneers in the hardware security space. In addition to UC San Diego's Kastner and CEO Oberg, Tortuga Logic's co-founders also include UC Santa Barbara computer-science professor Tim Sherwood, who is also a CSE alumnus (M.S., Ph.D. '03), and his former student, Chief Operating Officer Jonathan Valamehr, who earned all of his degrees from UC Santa Barbara.
Tortuga Logic’s products fill a gap between the intent of security IP building blocks and their actual deployment in full SoC designs. "Without these products, chips will continue to be built in ways that leave them vulnerable to hackers," said new VP Dauman. "Our goal is to ensure the chip’s final implementation does not expose a security hole that software will exploit.”
Related Links
Media Contacts
Doug Ramsey, (858) 822-5825, dramsey@ucsd.edu

